The Domain Name System (DNS) is a service which resolves real-world names to Internet Protocol IP addresses. My study notes should get you started on the material covered in 70-410, however, I’d strongly recommend you download the objectives from the Microsoft website, enjoy.
Domain Name System (DNS) – 70-410
At the top is the root, represented by a single dot (.)
Below the root nodes are the Top Level Domains (TLDs) .com .net .org. .edu
Each TLD branches out to other domains, referred to as Domain Names eg, Microsoft.com.
A host in the Microsoft.com domain would be, trigger.Microsoft.com. This is the fully qualified domain name (FQDN).
Dynamic DNS
Supported from Windows 2000 onwards, allows clients to auto update the DNS server records, or allows the DHCP server to update DNS with the IP’s it’s allocated to which HOSTS. (DDNS)
When setting up DDNS admins have 3 choices
- None – means your DNS server is non-dynamic
- Non-secure and Secure – Any machine can register with DNS (even if it does not have a domain account)
- Secure only – Only machines with accounts in AD can register with DNS
Non Dynamic DNS
Used by older client operating systems such as Windows 95/98, NT 3.51 & NT4
Sysadmins have to update the DNS database manually, reasonable for small to midsize companies or if you need to enter the TCP/IP information manually due to strict security measures.
DNS Queries – 3 types
- Iterative – Client asks DNS server for an answer, the server returns the best answer. If the server does not know the answer it may direct the client to another server through a referral.
- Recursive – Client sends a query to the name server and asks it to respond with the requested answer or an error message.
- Inversive – Uses PTR records, the client provides an IP address and then asks for the name. Makes use of the in-addr.arpa zone.
Cache and TTL
DNS Zones
The DNS zone is a portion of the DNS namespace of which the DNS server has authority. In the zone, there are resource records (RRs) that define hosts and other types of info that make up the database.
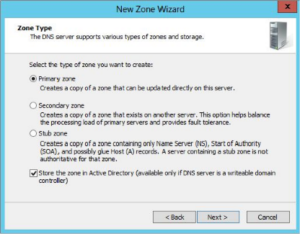
Zones are databases that store records. By choosing one zone type over another you are just choosing how the database works and how the data will be stored.
- Primary Zones – Responsible for maintaining all records, contains a primary copy of the DNS DB. Create and add Primary zones whenever you create a new DNS domain. There are two different types
- Primary Zones
- Primary Zones with Active Directory Integration (Active Directory Integrated Zones)
- Secondary Zones – Non-editable copies of the DNS database, used for load balancing or load sharing. Secondary zones get their database from primary zones.
- Active Directory Integrated DNS – Add-on to a Primary zone, after choosing to set up a primary zone check the box labeled “Store The Zone In Active Directory” (see below)
The database will be stored on the domain controllers and can not be loaded on Member Servers, which may be an issue for small companies.
Advantages of using Active Directory Integrated DNS Zones
- Full Fault Tolerance – Stored in Active Directory, so all AD DNS servers have access to the database.
- No additional network traffic – AD DNS zone data is stored in Active Directory, so any AD DNS server can respond to DNS requests.
- DNS Security – Can use secure dynamic updates, secure updates only allow machines with AD accounts to update DNS, stores and replicates through AD so data is encrypted as it sent from one DC to another.
Stub Zones
Similar to secondary zones, the database is a non-editable copy of a primary zone, however, stub zones only contain 3 records to identify the authoritative DNS server for the zone. They should not replace secondary zones or be used for load balancing and or redundancy.
Stub zones are useful when two large companies merge (example.com & example.net). Create a stub zone at each site pointing to the primary DNS server at the other site.
Global Name Zones
Provide support for single-label names, DNS names which do not contain a suffix like (.com .net)
Designed to be used with servers, used to map single-label CNAME (alias) to an FQDN. Global Name Zones are often used in place of a WINS server.
Zone Transfers & Replication
Secondary DNS servers receive zone updates from the primary zone via zone transfers. These occur in one of two ways
- Full zone transfers AXFR
- Incremental zone transfers IXF
When a secondary zone is first configured it receives a full zone transfer, this contains all the information in the DNS database (some always receive full transfers) and subsequent transfers are incremental.
The primary compares its version number with the secondary and only sends the changes that have been made. This significantly reduces network traffic.
The secondary can initiate a zone transfer, usually when the refresh interval time for the zone expires or when the secondary or stub server boots. Its possible to configure Notify Lists on the primary that send a message to secondary or stub servers whenever any changes to the zone database occur.
Active directory integrated zones do away with traditional zone transfers, instead they replicate across Active Directory will all other Active Directory information, secure & encrypted because it uses Active Directory security.
Stub Zone transfers with Zone replication – Only Active Directory Integrated Primary zones and Stub zones can configure their replication scope, which can be configured in two ways
- Through the DNS snap-in
- Command line tool DNSCmd
DNS Record Types
Start of Authority (SOA) Records – The first record in the database. It contains general parameters for the DNS zone including the identity of the authoritative server for the zone.
Name Server (NS) Records – Lists the name servers for the domain. Allows other name servers to look up names in the domain.
Host Record (A or AAAA) – Associate a hostname to IP address.
Alias Record (CANME) – Used to point more than one DNS record toward a host where an A record already exists.
Pointer Record (PTR) – Maps an IP address to hostname, the opposite of an A record.
Mail Exchanger Record (MX) – Specifies which servers accept Email for the domain.
Service Record (SRV) – Ties together the location of a service (like a domain controller) with information about how to contact the service
Load Balancing with Round Robin – Setup by creating multiple resource records with the same host but with different IP addresses, the DNS server will respond with the IP of one of the servers.
If round robin is enabled the first address in the database is returned and then sent to the end of the list, next the second name is returned and sent to the end of the list and so on.
Configuring a Caching-Only Server – These cache queries they resolve. When first started they have no information and build it up over time. They are easy to configure, after installing DNS simply make sure the root-hints are configured properly. No zone files, no transfers, the information they have is limited to queries they have resolved and cached.
Installing DNS
DNS can be installed as a stand-alone service on a member server on the network, or more commonly as part of the process of installing Active Directory.
Use Server Manager, Add role and features, Select DNS from the list, install additional features. Or use PowerShell.
DNS Forwarding
If the DNS server does not have an answer it may need to forward the request to another DNS server which has the answer, two types of forwarding
- External Forwarding – When the DNS server forwards the request to a DNS server outside the organisation
- Conditional Forwarding – Forwarded to specific DNS servers based on a condition. Test.com and test.net.
DNS Aging and Scavenging
The cleanup and removal of stale DNS records.
Monitoring and Troubleshooting DNS
Monitoring with the DNS Snap-in – Monitor and configure basic logging options.
Monitoring tab allows basic tests to be performed, simple query, or a recursive query
Debug logging tab – Monitor all inbound and outbound DNS traffic, packet type, transport protocol (TCP or UDP)
Useful tools
- Nslookup – Command line tool, perform query testing of DNS servers
- DNSLint – Command line tool, download from Microsoft.
- Used to diagnose name resolution issues
- Ipconfig
- DNSCmd – Allows you change the properties of DNS servers from the command line
- Can export the zone data
Troubleshooting the .(root) Zone – The root zone is the top level domain, Windows 2012 will build a .(root) zone when a connection to the internet cannot be found, because of this the .(root) may prevent access to the internet. The forwarding option and root hints will not be configurable. To enable forwarding or use root hints you must remove the .(root) zone
Issues with non-Microsoft DNS Servers – To complete zone transfers from Microsoft DNS to Unix based BIND secondary’s you must enable BIND Secondary’s on the Microsoft DNS Server.
So that concludes my study notes on DNS to cover the 70-410 Windows Server 2012 exam. I hope they help with the exam and as a real-world reference.
Thanks for reading
TSP Admin